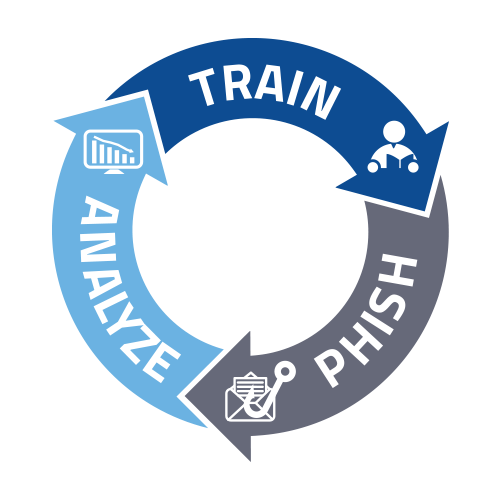
TRAINOn-demand, interactive and engaging training sessions keep your users interested in learning common traps and scenario based Danger Zones.
Contact Us To Learn More » PHISHSend year-round all-you-can-eat fully automated, simulated phishing attacks to your users. Access to a library of Phishing attack templates!
Contact Us To Learn More » ANALYZEAnalyze stats and graphs for both training and phishing. "Ready for Management"-worthy stats that are great for ROI!
Contact Us To Learn More » |
WHAT IS social engineering?
Social Engineering is the art of manipulating, influencing, or deceiving you in order to gain control over your computer system. The hacker might use the phone or email to gain illegal access. Phishing, Spear-phishing, and Whaling are forms of social engineering.
ransomwareRansomware is a type of malware that can be covertly installed on a computer without knowledge or intention of the user. It restricts access to the infection computer system and demands that the user pay a ransom to the malware operators to remove the restriction.
whalingWhaling is a phishing attack directed specifically at business owners and senior executives within businesses with the goal to trick someone into disclosing personal or corporate information. The content of a whaling attack email is often written as a legal subpoena, customer complaint, or executive issue. Whaling scam emails are designed to masquerade as a critical business email, sent from a legitimate business authority.
spear-fishingSpear Phishing is an email that appears to be from an individual or business that you know, but it isn't. It's from the same criminal hackers who want your credit card and bank account numbers, passwords, and the financial information on your PC.
|
CALL 334.358.6305
Website by BWS Technologies